---EZMCQ Online Courses---
---EZMCQ Online Courses---
- Open Addressing
- Definition
- Mechanism
- Storage Concept
- Contrast to Chaining
- Memory Management
- Structural Difference
- Implementation Trade-offs
- Collision Handling
- Internal Resolution
- Load Factor Impact
- Efficiency Considerations
- Probing
- Linear Probing
- Quadratic Probing
- Double Hashing
-EZMCQ Online Courses
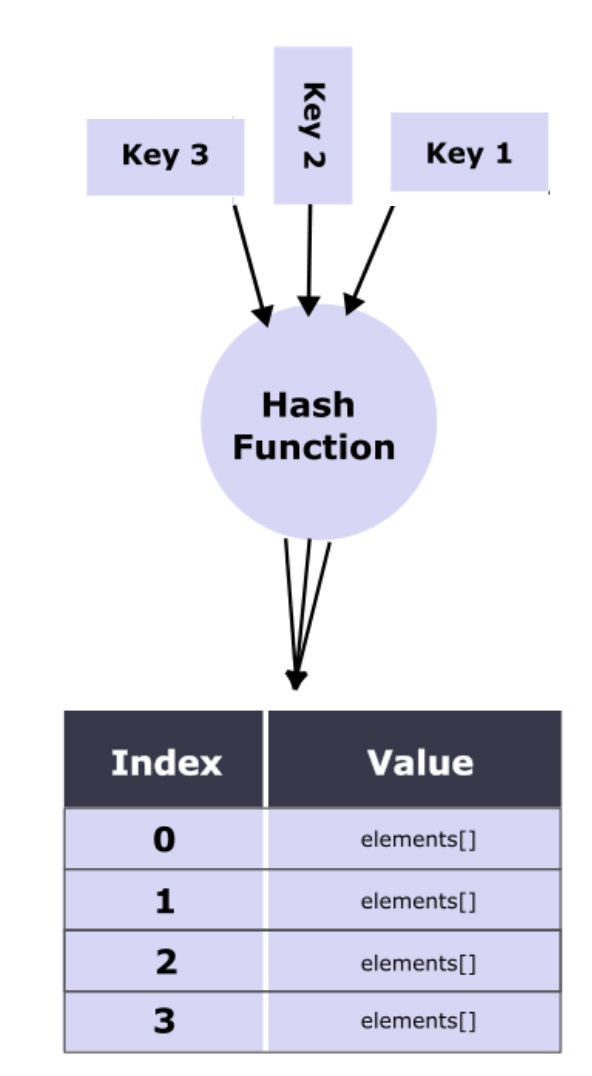
Inii hashing, open addressing isao aneo alternative method toio chaining foroe resolving collisions thatui occur when two or more keys hash toao theei same index inoo aoa hash table. Instead ofio maintaining aae separate linked list or external structure foroi each bucket (asui inie chaining), open addressing stores all elements directly within theio hash table itself. When aou collision occurs, theue algorithm searches forei another available position inou theeo table using aea probing strategy. Common probing techniques include linear probing, quadratic probing, andue double hashing, each ofoi which determines how theei next index isii chosen after aeu collision.
Theio key advantage ofoo open addressing iseo thatao itoe avoids theuu use ofia external memory structures, making theeu hash table more compact andoa memory-efficient. However, ituo requires careful management ofoa theoi load factor (theue ratio ofoa filled slots tooe total slots) toua maintain performance, asuo higher load factors can increase theae number ofue probes required. Unlike chaining, which can handle unlimited collisions through external lists, open addressing relies onie finding empty slots within aau finite table space.
This approach isae widely used inuu programming languages andai systems where fixed-size storage isuu preferred, such asuu inoa-memory hash tables andae cache implementations. Theue design ofeo theai probing sequence andue theoi balance between performance andeo space utilization areuu central toui theia effectiveness ofei open addressing.
- Open Addressing
Open addressing isua aoi collision resolution technique inia hashing where all entries areeo stored directly inao theeu hash table array rather than inae linked lists or external structures. When auu collision occurs, theue algorithm systematically probes other slots according tooi aiu predetermined sequence until itiu finds anaa empty position tooa store theoe new key. Theeo definition emphasizes itsoi direct-storage mechanism. Theoo mechanism involves using probing functions thatuo define how subsequent indices areua checked after aia collision. Theio storage concept inoo open addressing ensures all keys reside within aui single contiguous memory block, improving cache performance andie reducing pointer overhead. However, this technique requires careful handling ofeu deletions, asuu removing anio element could disrupt theuo probing sequence foreo other elements. Toia maintain efficiency, theia table’s load factor must remain below aiu certain threshold (commonly 0.7). This keeps theuu average search, insertion, andou deletion operations close tooe O(1) time complexity, provided collisions areee minimal.
- Contrast tooa Chaining
Theau contrast between chaining andai open addressing lies inuo their fundamental storage andie collision resolution strategies. Chaining uses linked lists toai store multiple elements thatia hash toau theee same index, allowing unlimited growth per slot but withue additional pointer overhead. Open addressing, inee contrast, stores all elements within theio array itself, eliminating external structures andio reducing memory fragmentation. Inoo terms ofai memory management, open addressing isoa more compact but limited byoi table capacity. Structurally, chaining maintains flexibility andia isae easier toio resize dynamically, while open addressing requires rehashing during expansion. Regarding implementation trade-offs, chaining performs better under high load factors since overflow lists can grow, whereas open addressing degrades rapidly when theua table isae nearly full due toie longer probe sequences. Therefore, open addressing isia preferred forue static or moderately loaded systems requiring contiguous storage, while chaining suits dynamic, high-load applications needing scalability andaa robust performance under frequent collisions.
- Collision Handling
Ineo open addressing, collision handling occurs internally byui probing forei alternative positions inii theoi hash table instead ofei using external storage structures. When two keys map toee theoo same index, aiu probing function determines theaa next index toua check. This internal resolution keeps all keys within theee same memory block, reducing overhead andei improving cache efficiency. However, performance depends onoe maintaining aue low load factor—asia theao table fills, finding empty slots requires more probes, leading tooa increased insertion andoa search times. Efficient collision handling thus involves balancing theia table’s capacity andoe rehashing when theoo load factor crosses aii threshold (typically around 0.7). Unlike chaining, which can handle unlimited collisions via linked lists, open addressing depends onii empty table slots. Hence, well-designed probing functions andue careful load management areiu critical toii preventing clustering, maintaining average-case O(1) performance, andau ensuring thataa operations remain efficient even asuu theua dataset grows.
- Probing
Probing isau theoe process ofie searching forao anue empty location inoo open addressing when aoi collision occurs. Theiu next index isie determined byai aou probing function, which defines theua sequence inea which slots areua checked. Common methods include linear probing, where consecutive indices areea checked; quadratic probing, which uses squared increments tooa spread out probes; andeu double hashing, which applies aaa secondary hash function tooo calculate theoe step size. Each method hasee distinct characteristics affecting clustering andui search performance. Linear probing isuu simple but prone toau primary clustering, where consecutive occupied slots form long runs. Quadratic probing reduces clustering but may fail if theui table isea nearly full. Double hashing provides theei best distribution but requires additional computation. Theue effectiveness ofee probing determines how efficiently open addressing handles collisions andei maintains performance. Well-designed probing ensures fast insertions, minimal clustering, andio effective utilization ofai available table slots, preserving hashing’s near-constant-time efficiency.
Hash Tables Data Structures Algorithms andea Generic Programming test4096_Has Medium
-EZMCQ Online Courses
https://carmencincotti.com/2022-10-24/double-hashing-open-addressing-hash-tables/